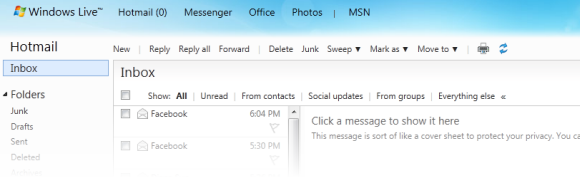
I haven’t seen anything published about this yet, but I noticed today that Windows Live Hotmail seems to be authenticating incoming e-mail using DKIM in addition to Sender ID.
Background
In the past, Hotmail has verified the authenticity of incoming e-mail through Microsoft’s proprietary version of Sender Policy Framework called Sender ID. Both of these projects were designed to verify that the computer sending the message, as identified by the originating IP address, is authorized to send e-mail on behalf of the named sender.
A typical SPF policy, specified through a TXT record in DNS, might say
v=spf1 ip4:208.97.132.0/24 -all
This means that only IP addresses in the 208.97.132.1–208.97.132.254 range are allowed to send e-mail on behalf of this domain. (The Sender ID policy would look similar, but starting with spf2.0/pra.)
Hotmail’s policy has been to verify all incoming e-mail using the Sender ID framework. This theoretically reassures users that authenticated e-mail definitely comes from the named sender, reducing the likelihood of header forgery. If an e-mail does not pass Sender ID verification (softfail) and has other signs of being forged, it will likely be classified as junk.
A valid e-mail is marked with these headers:
X-SID-Result: Pass
X-AUTH-Result: PASS
If the organization’s policy uses the strictest policy (-all), and the message does not pass Sender ID validation, and the organization has submitted its Sender ID records to Microsoft, invalid e-mail sent to @live.ca and @live.com domains are rejected. As far as I am aware, this protection is not applied to @hotmail.com accounts.
From SPF to DKIM
The problem with SPF is that it doesn’t verify much. All it tells us is that an e-mail comes from the right computer—not that an intermediate server hasn’t tampered with it. In addition, SPF only really validates the From: or Sender: headers.
Besides, many large service providers cannot implement a strict SPF/Sender ID policy because users may be sending e-mail through other servers. (For example, I might use my ISP’s SMTP servers to send e-mail from my Windows Live Hotmail address; a strict SPF/Sender ID policy would mark those e-mails as junk.)
DKIM, however, encompasses the contents of the message body, in addition to the headers. It does not necessarily require the e-mail to come from a certain IP address. Using public key cryptography, it allows organizations to take responsibility for sent e-mails by verifying that the e-mail came from an authorized source, similar to the way secure servers connect over TLS/SSL.
Implementing DKIM means that all outgoing e-mails are signed using a private key; the signatures are then checked by compatible software against the public keys published in DNS. Each domain can have multiple DKIM keys, allowing multiple sending systems to sign outgoing e-mails independently.
A sample DKIM signature looks like this:
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed;
d=frederickding.com; s=google;
h=domainkey-signature:mime-version:from:date:message-id:subject:to
:content-type;
bh=b3wR4p4G21l92tc0ahioopi7atMwDp2wkaQb/uOL65E=;
b=YJ6nD3Nx5hgwRhYppb/n2g5lQxA5jzFvYEJ0dR4dtkRFv14GVJWStQXwwZryGuujC/
v4ve5ZE3ZAEAtv5hCj99ZLAfR52rskpbitso+106M8uQvryLyuLSnX1mrk6JaDFLMr8V
qHmCEZUF5+cnWEYSwlLo1T8hntgN28hj8OyJY=
DKIM actually requires a lot more work for organizations to implement, as it requires additional DNS lookups and (perhaps) expensive cryptographic calculations. A decade ago, it would have been unfeasible to implement this on an organization as large as Windows Live Hotmail.
Hotmail today
Today, the inexpensive cost of processing power makes it possible for Hotmail to validate DKIM. Yahoo! has been doing this since the beginning, as it was the source of this technology. Gmail, too, has been validating DKIM for some time. (Both Yahoo! and Gmail sign outgoing e-mail with DKIM signatures, and Google has made this possible through its Google Apps service for companies as well.)
While Windows Live Hotmail has always validated Sender ID, today I noticed the addition of a new e-mail header:
X-DKIM-Result: Pass
This is good news.
Conclusion
To summarize a post’s worth of babbling, this means that Windows Live Hotmail is taking additional steps to combat e-mail forgery, phishing and spam. A step forward for everybody.